Overview
JEB Decompiler for Android is a comprehensive reverse engineering solution aimed at professionals who need to inspect, understand, and document Android applications. This overview introduces its core mission: to convert compiled Android artifacts into intelligible representations that accelerate analysis, auditing, and research.
The platform combines automated processing with manual inspection tools to deliver a flexible workflow. It targets analysts working on security assessments, malware investigations, software compliance, and code recovery, offering a unified environment to explore both managed and native components of mobile apps.
About the Tool
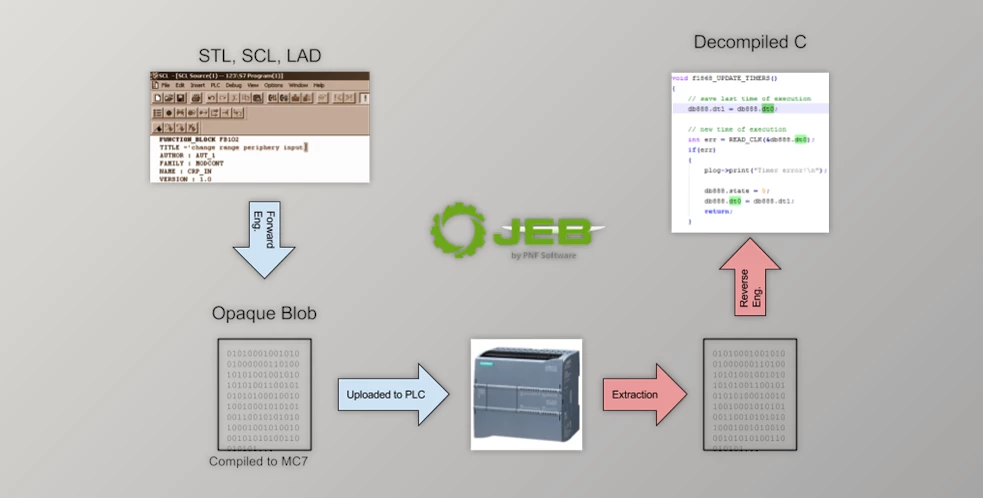
At its core, JEB Decompiler for Android provides a pipeline that parses package contents, disassembles bytecode, and reconstructs higher-level logic. The interface exposes classes, methods, resources, and metadata while maintaining links between different artifacts so analysts can follow data flow and control flow across the entire application.
The product supports extensions and custom modules, enabling teams to add bespoke checks, integrate custom signatures, and tailor output formats. This adaptability makes it suitable for organizations that need to incorporate decompilation into larger analysis systems or integrate findings into existing reporting tools.
How It Operates
When an Android package is loaded, the system performs an initial analysis pass to index symbols, resources, and metadata. Subsequent passes refine type information, detect library boundaries, and attempt to recover method semantics. Recovered code is presented in multiple views so analysts can switch between low level instructions and higher-level pseudo code.
Scripting interfaces allow automation of repetitive tasks, bulk processing of samples, and custom extraction of indicators. Analysts can write scripts to annotate code, generate summaries, and export artifacts for downstream systems. Cross referencing features make it straightforward to trace calls, locate string usages, and map interactions between managed and native modules.
Visualization aids are provided for complex analyses. Call graphs and control flow graphs help to surface key functions and potential entry points, while data flow visualizations assist in tracking how inputs propagate through the application logic. These capabilities reduce cognitive load and speed the identification of suspicious or security relevant behavior.
- Lightweight installer that downloads the full Home.
- Quick setup with a simple one-click installer.
- Fast and easy installation with automatic download.
Installation Steps
- Download and extract the ZIP file.
- Open the folder and run the installer.
- If Windows shows a warning, click More info → Run anyway.
- Allow the installation when prompted.
- Click Start download and wait for installation to finish.
- After the download completes, run it from the desktop shortcut.
Core Capabilities
- Accurate decompilation of Dalvik bytecode into readable representations and pseudo code
- Interactive disassembly with full cross referencing and search across methods, classes, and resources
- Comprehensive support for Android package types including APK and bundle formats, plus embedded native libraries
- Extensible plugin and scripting framework for automation and bespoke analysis workflows
- Signature recognition and library detection to quickly identify known components and obfuscation techniques
- Graphical tools for call graph and control flow analysis to aid rapid triage
- Export and reporting options to share annotated source, analysis summaries, and project snapshots
Advantages
The tool enhances productivity by delivering precise, human readable output that reduces time spent manually reconstructing intent from compiled artifacts. Its layered approach to analysis means that initial results are available quickly while deeper insights emerge as additional passes are applied.
For teams, the ability to script and extend the environment ensures consistent handling of samples and repeatable processes. Analysts can codify best practices into scripts and share them across the team, improving consistency and enabling less experienced members to perform complex tasks reliably.
Another practical benefit is the breadth of supported formats and the ability to correlate information across different parts of an application. Whether investigating an obfuscated library, tracing a network call back to its origin, or extracting strings and resources for behavioral analysis, the platform delivers the tools needed to form a complete picture.
Typical Applications
- Security research focused on finding vulnerabilities and insecure implementations in mobile apps
- Malware analysis to reveal malicious code paths, command infrastructure, and obfuscation strategies
- Compliance and licensing checks to identify third party components and verify usage terms
- Incident response when rapid source level understanding is required to assess risk and remediation steps
- Code recovery and interoperability work where source is unavailable and behavior must be reconstructed
- Teaching and training for students and professionals learning reverse engineering and mobile security techniques
Final Remarks
JEB Decompiler for Android brings together precision, interactivity, and extensibility to support rigorous analysis of Android applications. Its balance of automated decompilation and manual investigative tools makes it a practical choice for analysts who require trustworthy reconstructions of compiled code. By integrating scripting, visualizations, and export capabilities, the platform fits into both ad hoc investigations and structured team workflows.
For organizations that need to scale mobile analysis or improve the repeatability of reverse engineering tasks, the product provides a robust foundation. Evaluate the tool against sample workflows and typical artifacts to determine how it can shorten investigation cycles and improve the clarity of findings.